Time-consuming questionnaires, overwhelmed vendors, limited resources: discover how AI and Board of Cyber's new solutions are transforming Third Party Risk Management.
TPRM (Third Party Risk Management) has become a constant source of friction for security teams. Between sending questionnaires, endless follow-ups, and analyzing heterogeneous responses from hundreds of third parties, the process is reaching a breaking point. At the "Automate Your Vendor Questionnaires with AI" workshop at Forum InCyber 2026, Sylvain Lefeuvre, Deputy Managing Director, and Julien Steunou, Chief Product Officer of Board of Cyber, laid out how to break free from this technological deadlock.
The TPRM Gridlock: When Volume Strangles Security
The problem stems not just from tooling, but from resource saturation. With the arrival of NIS2 and DORA, CISOs must now assess not just 20 or 50 critical vendors, but their entire digital service supply chain. As Luc Declerck points out, "there is a lack of resources on these topics" when it comes to scaling up.
This saturation creates what Julien Steunou calls a gridlock:
- On the client side: GRC teams receive mountains of documents they no longer have time to analyze thoroughly.
- On the vendor side: They are overwhelmed by questionnaires that are 80% redundant but presented in different formats. "A vendor's primary job is not to spend all day filling out questionnaires," reminds Luc Declerck.
The challenge is therefore no longer about which questionnaire to use, but about solving the documentary burden problem. Today, compliance has become a static, time-consuming administrative "snapshot," whereas the original goal is resilience. Without automation to absorb this workload, the system seizes up and loses its security value.
AI in Service of TPRM: 4 Concrete Levers
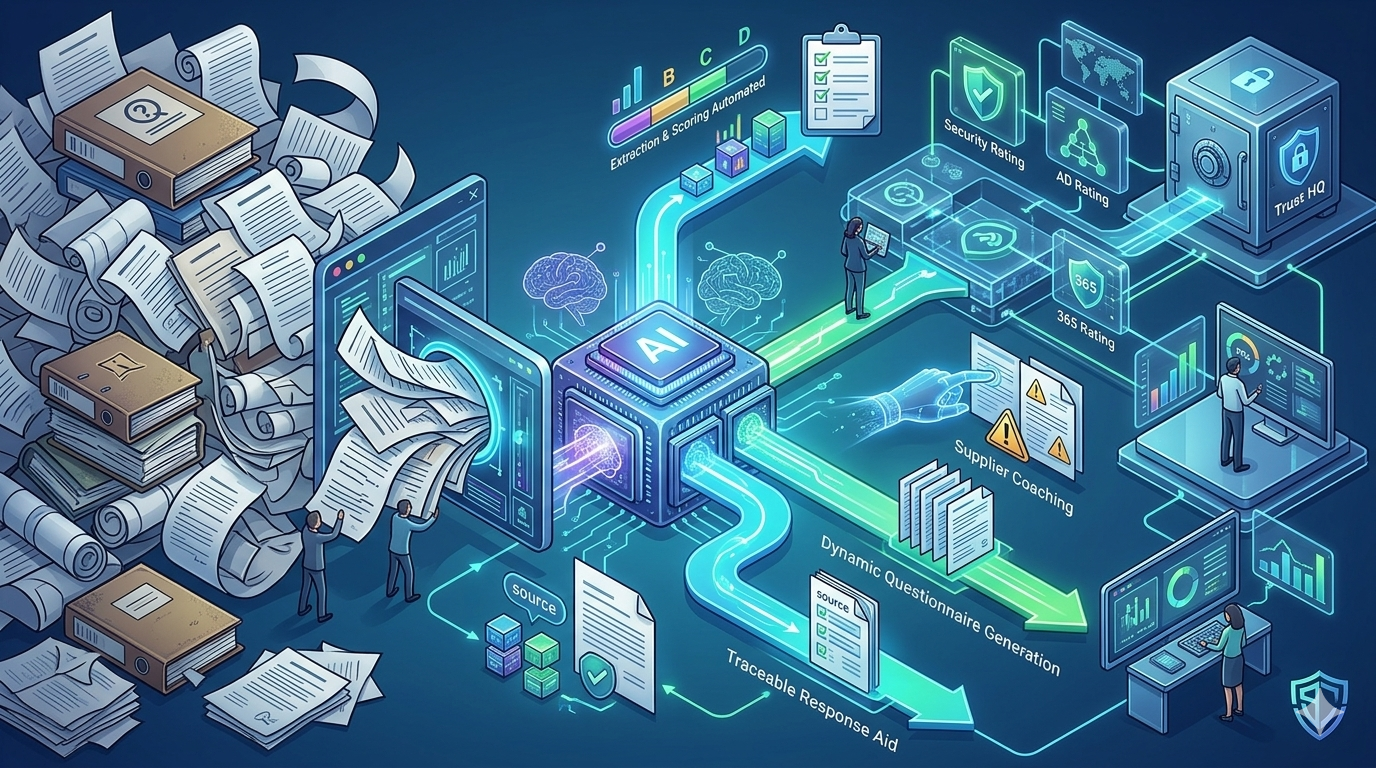
To break this dynamic, Board of Cyber has structured its technological response around four pillars leveraging LLM and RAG (Retrieval-Augmented Generation) architectures.
1. Automated Extraction and Scoring
The goal is to capitalize on information already present in the vendor's security documentation (ISSP, certifications, pentest reports). Julien Steunou explains the approach: "The idea is to combine the efficiency of LLM/RAG processes to extract structured information, with more deterministic approaches to produce a score." The performance speaks for itself: where a GRC analyst would spend days combing through a file, the Risk Rating solution processes a corpus of 47 documents in just a few minutes. The system identifies covered control points, as well as inconsistencies between the various documents provided.
2. Vendor Coaching
AI actively guides third parties by highlighting their "blind spots." For example, cyber insurance is a control point frequently missing from vendor documentation. The tool flags these gaps or internal contradictions, allowing the vendor to correct their posture before the final assessment.
3. Dynamic Questionnaire Generation
Instead of a standard 150-question questionnaire, AI dynamically generates a tailored set of questions. These focus exclusively on the grey areas that documentation failed to address. For a mature vendor, this represents a significant time saving and a far more qualitative approach.
4. Response Assistance
This lever directly benefits the vendor by preparing sourced responses based on their own document repository. Traceability is complete: "If an element has been included in a response, it's because it is sourced from a document," specifies Julien Steunou. This virtuous cycle automatically enriches the documentary repository for future assessments.
A Platform for a 360° View
What sets Board of Cyber apart is its ability to combine three complementary building blocks, adapting the level of investigation to the actual criticality of each third party. This architecture makes it possible to build a coherent and scalable TPRM program:
-
Security Rating: continuous, large-scale assessment. This is the essential tool for vendor classification. By analyzing the external attack surface using public data, it scores thousands of third parties. It serves as the first filter to quickly identify those presenting an observable cyber risk.
-
Trust HQ: managing critical audits. For vendors deemed strategic, the platform enables in-depth, customized audits. Evidence submission takes place in a secure environment through SecNumCloud hosting, ensuring maximum protection of sensitive data shared by third parties.
-
Risk Rating: AI-powered automated assessment. AI streamlines the review of key control points (cyber and GRC) to extract evidence and generate a score within minutes. Beyond assessment, Risk Rating produces a concrete action plan for the vendor, turning the audit into a lever for continuous improvement.
Conclusion: From "Snapshot" to Continuous Monitoring
The ultimate goal championed by Board of Cyber is to transform the point-in-time audit into a continuous assessment. Instead of an annual "snapshot" that freezes compliance in place, AI can continuously absorb documentary updates. "It makes the process much more dynamic, with more value for both auditors and vendors, lifting the entire ecosystem," concludes Julien Steunou.